Building a Resilient Voice Authentication Strategy for 2026
Introduction
Enterprises today are transitioning from simple chatbots to agentic AI capable of end-to-end resolution. And, as we move toward 2027, the stakes for these transitions have shifted; with mobile voice fraud projected to cost enterprises $415 billion by 2028, the integrity of identity has become the most critical engineering requirement. So, while Virtual Agents can handle all front-line requests such as checking medical records, moving money between accounts, or changing personal passwords, before it can execute a high-value transaction, it must first solve one of the most complex variables in system design: user authentication. For top global healthcare firms we support, this isn't just a technical preference, it's a multi-billion dollar security mandate.
Voice authentication, therefore is no longer just a hurdle to be cleared at the start of a call. In our view, it is a dynamic security layer that must bring together phone data and customer records to run precise identity checks. We’ve moved past simple gates based on basic details like birthdays or zip codes. We now need a strategy that not only confirms identity in the background while adhering to the principle of least privilege - i.e. allowing minimal access to data based on the function required to be performed.
In this blog, we will explore the technical challenges of voice authentication and provide a blueprint for designing a secure strategy that balances safety with the ability to deliver seamless customer experience.
The Technical Challenges of Voice Authentication
Building a secure authentication process for voice is notably more complex than for text-based channels. It requires solving specific engineering problems such as technical limitations of voice technology while accounting for customer limitations around how they actually behave during a phone call. When we began architecting our approach, we focused on five specific engineering hurdles:
- Capturing precise alphanumeric data over voice is inherently difficult: STT/TTS models are optimized for natural conversation, not for rigid data. We’ve found that even minor background noise could cause models to swap "B" for "D," leading to false rejections. Hence, building specialized models that can handle structured strings is imperative to minimize transcription errors.
- Relying on telephony metadata is inherently unreliable: Phone numbers alone can’t be treated as final proof of identity anymore. For any high-value, irreversible transactions like moving money, we believe the automation architecture must require a secondary digital factor to ensure the caller is truly authorized.
- Managing system latency during security handshakes is a constant struggle: We’ve seen too many security checks fail because of dead air. Therefore, optimizing the connection between our voice engine and security records was absolutely necessary to ensure these checks don't interrupt the natural flow of speech.
- Minimizing cognitive load is a major design hurdle: When we designed our workflows, we had to account for the fact that callers hate opening apps mid-call. Our goal was to design authentication that minimizes cognitive load to ensure the highest possible completion rate.
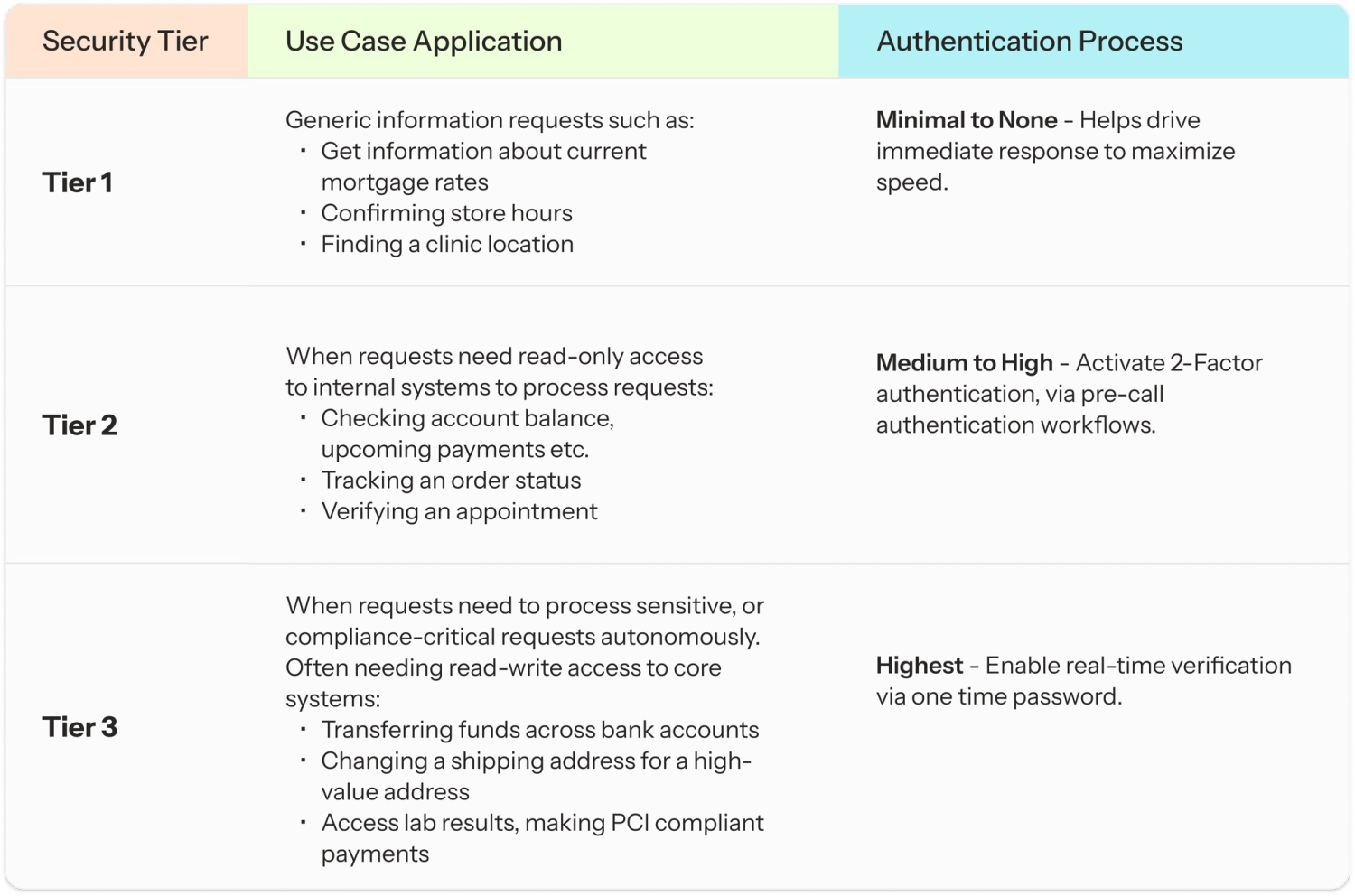
- Balancing security gates with resolution speed is a delicate trade-off: Every security step you add increases the time it takes to solve the customer's problem. And, we realized that this is the hardest balance to strike. Our approach is to use a tiered strategy: we only trigger the most difficult security steps for high-risk requests, keeping the experience fast for simple questions.
Architecting a Tiered Authentication Strategy
A secure voice strategy is most effective when it is part of the natural flow of the conversation rather than a stand-alone security barrier. We designed our platform to ensure secure and compliant authentication at every step of the interaction, across all touchpoints. This allows brands to move from a pass-fail security mindset to a fluid experience where trust is built and verified in real time. Here is how we approached the implementation of three key models within the Level AI platform:
1. Voice Biometrics: Verification via Biological Signature
This workflow analyzes the unique physical and behavioral characteristics of the human voice to verify the individuals based on their biological voiceprint. Voice biometric based authentication could be of two types:
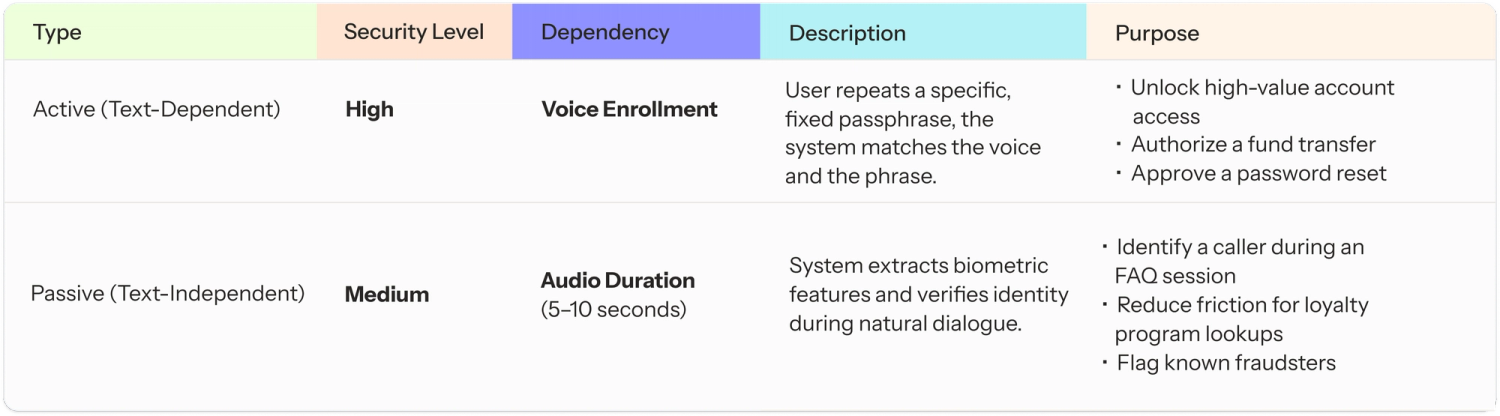
While voice biometrics is a foundational feature, for highly regulated sectors, Level AI seamlessly integrates with advanced third-party biometric systems, such as Pindrop, to leverage their specialized fraud detection and liveness capabilities for enhanced security and compliance.
2. Pre-Call Authentication
As the user dials in, even before the conversation begins, our platform can establish a verified user status to reduce average handle time for requests and eliminate the need for added customer effort.
- Pre-call Automation Workflows: We built hybrid workflows that capture Caller ID as well as telephony data to trigger a deterministic workflow as soon as the incoming call is detected. The fetched data is then verified by directly accessing customer records within the CRM via API. We use this to also retrieve other vital information such as the account owner name, loyalty status, or existing service tickets. By verifying these details in the background, Level AI platforms enable CX leaders to personalize the greeting and anticipate user intent before a single word is spoken.
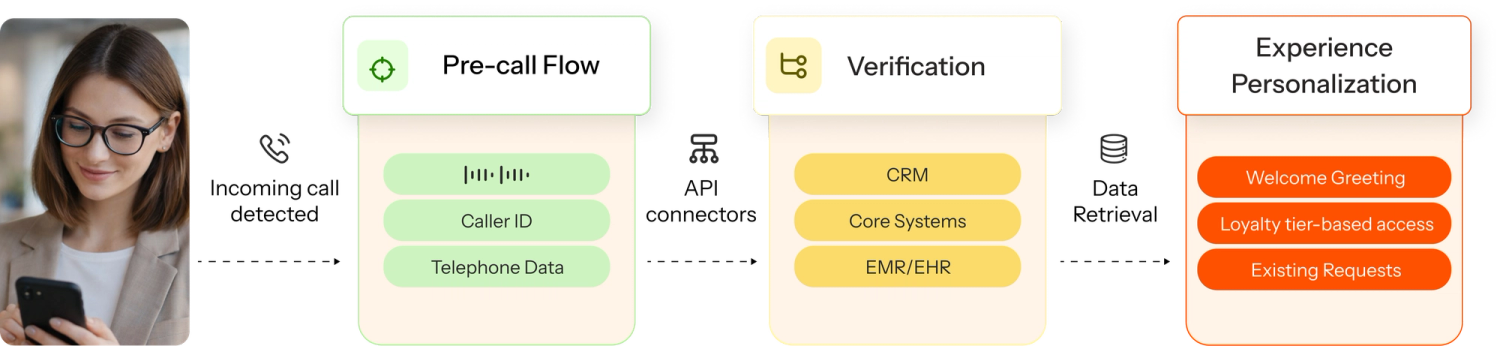
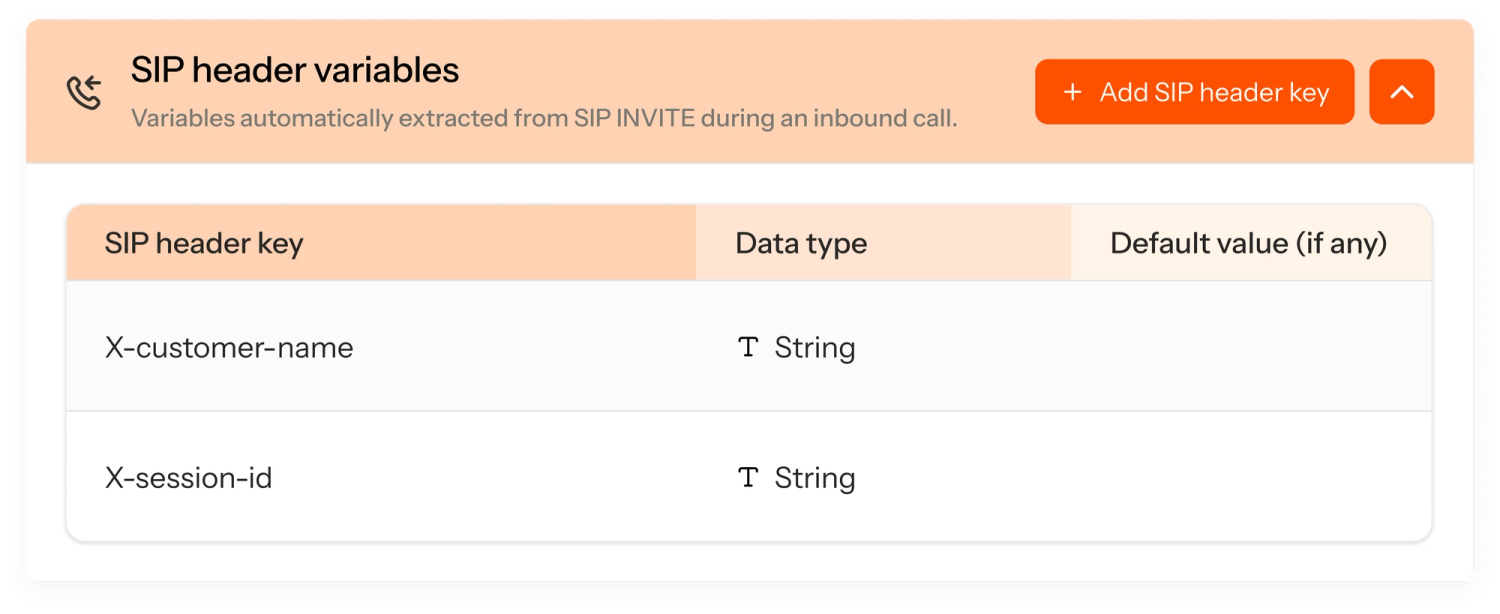
- SIP Metadata-based Verification: For enterprises with complex telephony systems, we enabled the ingestion of unique security identifiers directly while configuring the virtual agent. The systems check this SIP metadata for specific identifiers, such as a valid session ID from a mobile app. If the necessary markers are present, our workflow assumes the caller is authenticated and skips redundant questions. If they are missing, it intelligently triggers a relevant identity verification flow based on the data it already has.
3. Real-time Mid-conversation Authentication
While pre-call checks handle known users, mid-conversation authentication allows the virtual agent to verify the caller before proceeding with any sensitive request. This ensures that every transaction is backed by real-time validation, protecting both the enterprise and the customer from unauthorized access.
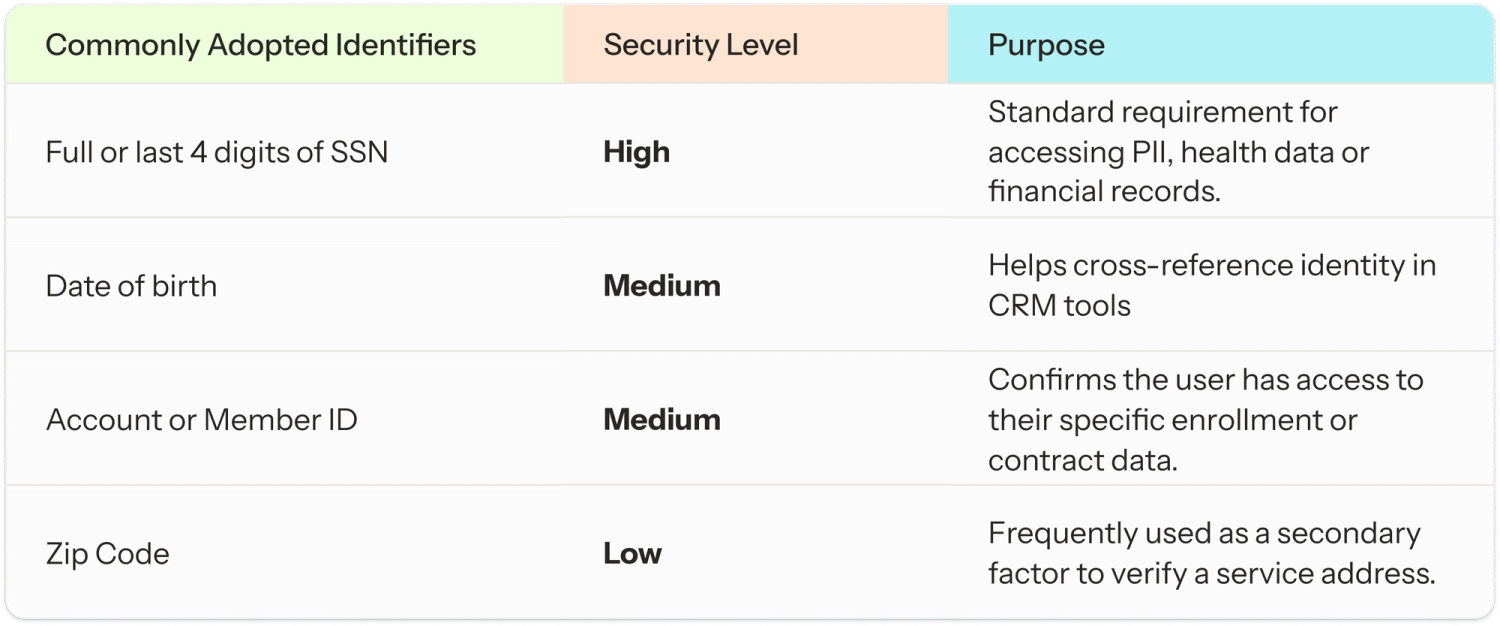
- Multi-Factor Authentication (2-FAC, M-FAC): When we designed our workflow builder, we used agentic nodes so that CX teams can provide detailed natural-language instructions with ease, to collect specific identifiers and trigger authorized next steps. This ensures that the agent can probe for details, confirm they are correct, and politely decline account access until all criteria are met. Here are some of the most common identifiers leveraged we noticed were leveraged by brands:
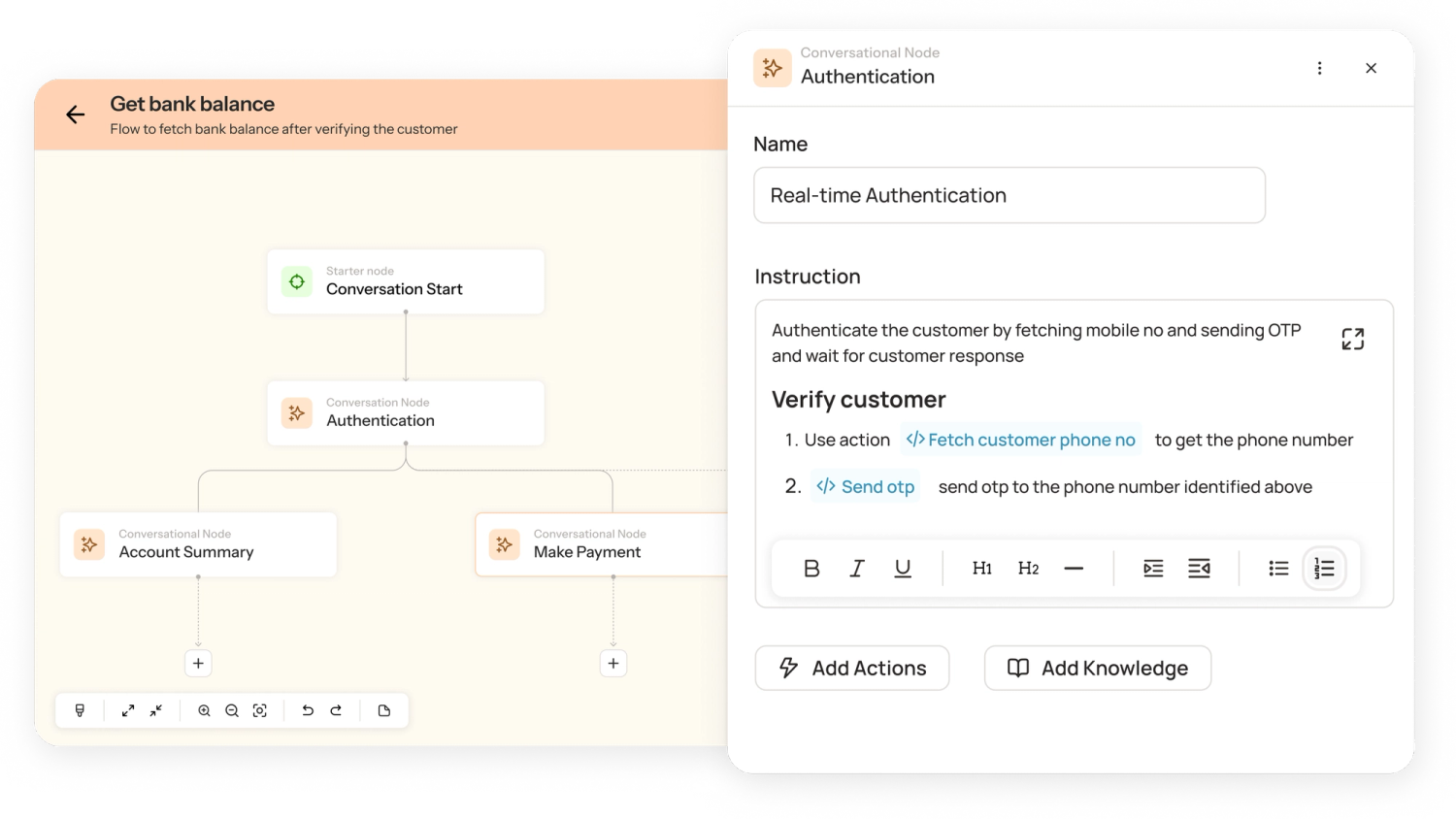
- One Time Password-based Verification (OTP): To solve for high-security environments, we made sure our system could trigger real-time code verification. Within the agent configuration, CX experts can specify exact execution steps and instructions for this skill. This allows the Virtual Agent to send an SMS or email, wait for the user to provide the code, and verify it against the system without any manual intervention.
- Strategic Step-up Logic: An important aspect while designing our AI was for it to have the ability to escalate security only when the context of the call changes. A user might start by asking a general question but later decide to make a payment. We designed a system to move from a low-trust state to a high-trust state mid-conversation without forcing the user to restart the call. We achieved this by combining rule-based logic for triggering flows with agentic nodes that perform the heavy lifting of authentication.
To ensure these steps are accessible to everyone, we also had to ensure that our platform supports a flexible input methodology. End-users can choose to speak their details naturally, and brands could capture security identifiers directly over voice or via DTMF based input received as users type them directly on their phone keypad. This ensures 100% accuracy for complex codes while offering a private way for end-users to provide information in public spaces.
3-Step Framework for Choosing Your Authentication Strategy
To ensure the automation strategy is both secure and efficient, we recommend that CX leaders align the depth of the verification process with the specific risk profile of each customer request. And to solve for that, we created a quick 3-step guide to select the right authentication strategy based on the nature of the task, ensuring that security measures remain proportionate to the sensitivity of the operation.
Closing: Securing the Future of Voice CX
The shift toward AI-driven voice support represents a massive opportunity to reduce costs and increase efficiency, but it also introduces a new frontier of security risks. As we see it, the goal of a modern voice strategy is simple: make it impossible for fraudsters to break in, while making it invisible for end-customers to get in. By combining tiered authentication, risk-aware workflows, and real-time step-up logic, we orchestrated a high-fidelity system that delivers a voice experience that is as secure as it is seamless.
In addition to the authentication frameworks we’ve covered, our platform also provides intelligent voice activity detection, PII redaction for HIPAA and PCI compliance, and full-spectrum encryption for data in transit. By integrating these capabilities into a single intelligence layer, we’ve seen our partners move from defensive, pass-fail security to a resilient system that protects the enterprise while honoring the customer’s time.
Talk to us to learn how you can design secure authentication flows for end-to-end compliance.

Frequently asked questions
Q1. How accurate is voice biometrics compared to other authentication methods?A. Voice biometric authentication is highly accurate when implemented correctly, often achieving 95–99% accuracy under controlled conditions. Compared to traditional identity verification methods like passwords or PINs, voice authentication offers stronger security because it uses unique vocal traits that are hard to replicate. However, accuracy depends on factors like audio quality, background noise, and the use of liveness detection in AI voice authentication systems.
Q2. Can voice biometrics be spoofed with recordings or deepfakes?A. Basic voice verification systems can be vulnerable to replay attacks or AI-generated deepfakes. However, modern voice security systems use liveness detection and behavioral analysis to prevent spoofing. Advanced AI voice authentication solutions analyze speech patterns, tone variations, and real-time responses, making it significantly harder for attackers to bypass authentication using recordings or synthetic voices.
Q3. What about users with accents, speech impediments, or health conditions?A. Modern voice biometric authentication systems are designed to adapt to diverse speech patterns, including accents and minor speech variations. However, significant changes due to illness or health conditions can impact accuracy. Leading voice authentication systems continuously learn and update voice profiles, improving identity verification reliability over time while maintaining inclusivity.
Q4. How does voice biometrics handle multilingual customers?A. Advanced voice biometric authentication systems are language-agnostic because they analyze vocal characteristics rather than language content. This makes voice verification effective across multiple languages. For global businesses, this is a major advantage over traditional identity verification methods, especially in AI voice agents caller authentication methods where customers interact in different languages.
Q5. Can voice biometrics work with poor audio quality (phone calls, noisy environments)?A. Yes, but performance may vary. Modern voice security systems are optimized for telephony and can handle compressed audio from phone calls. Noise reduction and signal processing techniques improve voice authentication accuracy, but extremely poor audio quality can still impact results. High-quality AI voice authentication systems are trained specifically for real-world call center environments.
Q6. Is voice identification security a reliable method for banking over the phone? How does it compare to using passwords or PINs?A. Yes, voice authentication is increasingly used in banking because it offers stronger voice security than passwords or PINs, which can be stolen or guessed. With proper safeguards like liveness detection, voice biometric authentication provides secure and seamless identity verification, reducing fraud while improving customer experience
Keep reading
View all